Real time reports fast
Whether your developer needs to create an instant report about their software project's bill of materials or maintain ongoing compliance for security or legal due diligence, Meterian delivers both. Get reports to send to your legal counsel and information security officer (CISO) in HTML/PDF, or in JSON format for your favorite developer tool as frequently as you wish.

Easy to integrate
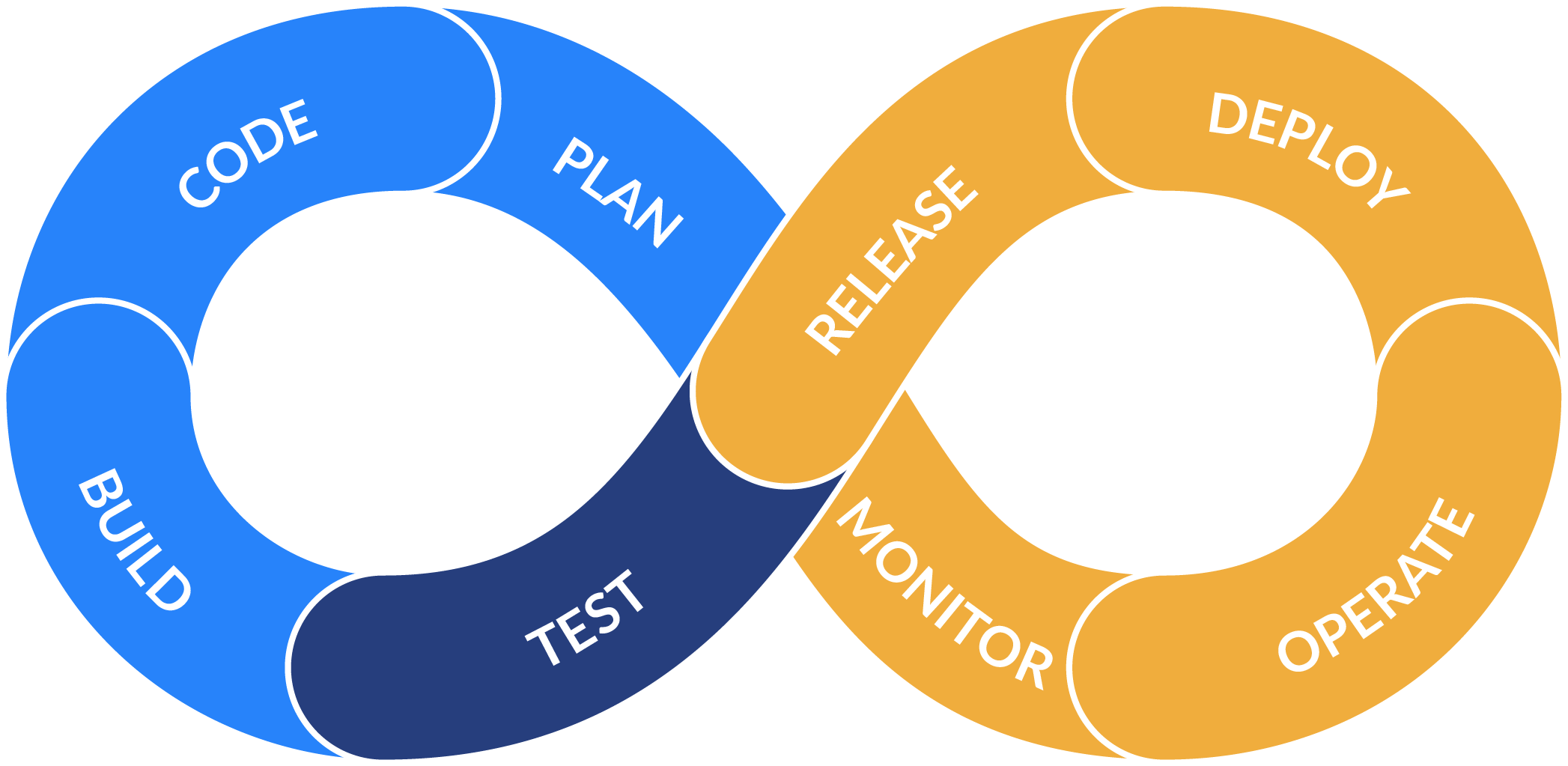
Meterian can be used in an instant locally on the developer's computer or as part of a continuous integration (CI) pipeline to see security, stability and licence risks immediately. Meterian fits right into the developer's workflow so the builder mindset has the company's security and legal risk policy enforcement baked in.
Reduce security debt
As the pace of software development in your company increases, Meterian prevents bugs, vulnerabilities and compliance risks from piling up. Avoid costly financial and legal damages as a result of risks in your software assets. Meterian's fast, automated solution frees your developers from repetitive and manual research work of analysing the dependent components. Run Meterian continuously to stay informed of known risks in your apps' dependent components.

HOW IT WORKS
The scanner will start to gently download the website contents from the address you entered onto our server, in a way similar to what a search engine crawler does when indexing. Then the meterian scanner will be executed against such contents to discover, analysing and classifying the content. It will look for vulnerable or outdated components, and for any component licensed in a non-friendly way, reporting back what it did find.
No. This is not a load/stress test or a penetration test, we are just scratching the surface of your website looking for tiny signatures that allow us to identify the components used. We will analyse the same content only once each analysis, so it's pretty much like somebody who patiently visits all the contents of your website.
The complete report will provide a complete list of all the components and for each of them any possible vulnerability, a complete upgrade path, and the full list of available licenses, when available.
Yes. Once you got access to the complete report, submitting the request form, you will also be able to request it to be deleted.
This may take up to two minutes, especially on big websites, but normally much less. If you do not want to wait, do not worry: the scan will be executed in the dashboard, and you will just need to check later.
No. If something is found you can be pretty sure it's there, but this is not a comprehensive analysis. In order to do that, we would need to work on the source code of the website, something your development team can do using our command line scanner. It is available here on a free trial for one project.
Yes. Each analysis will eventually have the opportunity to appear in the samples carousel. As the website is public, also the reports are, and anybody can analyze any website.